Understanding the strategic benefits of communications technologies
The contemporary landscape of conflict has evolved past the boundaries of traditional warfare, and is now primarily decided by modern technologies. Among the advances in destructive capacity and automation, communications is increasingly becoming a key area of strategic dominance. Tested and implemented in sensitive environments, these advances reveal a growing paradox between clandestine operations and public infrastructure. The public telecom infrastructure billions use to communicate is supported by aging interoperable infrastructure that is fundamentally insecure and susceptible to exploitation. Conversely, intelligence agencies, criminal syndicates and state backed cyber criminals enjoy bespoke private networks that are superior to anything available to the general public.

This divergence is not a coincidence. It is the result of different priorities. Public telecom providers value interoperability over updating outdated technologies and consumers value convenience over secure communications. Meanwhile, shadow organizations prioritize the unconstrained adoption of cutting edge open-source technologies to ensure operational resilience. Nowhere is this more apparent than inside criminal organizations that have fought against pervasive surveillance from adversaries and law enforcement. By building their own shadow infrastructure these groups have effectively de-coupled themselves from the global communications grid, forcing their adversaries to adopt increasingly invasive techniques for infiltration.
Advanced technical capabilities have become essential for modern clandestine operations. These groups do not merely use technology; they iterate with speed and often end up pioneering new technologies. The distrust of public cellular networks is deeply rooted in the collaboration between law enforcement and telecom providers. In the public sphere, calls and messages generate metadata and content that can be subpoenaed or intercepted through mass surveillance.
Equally as important, public networks are susceptible to infiltration from rival criminal organizations who can monitor one another’s communications. This leads to a constant cycle of counter intelligence that fuels innovation. It’s true that legal entities are susceptible to these types of attacks, but the incentives and motives for exploiting these entities are fundamentally different. The competitive nature of illicit organizations fuels a particular type of security forward innovation.
Criminals don’t trust the security of public telecommunications networks. You shouldn’t either.
The most significant vulnerabilities in public telecom infrastructure aren’t peripheral, they exist in the bedrock of PSTN and cellular services.
SS7 and Diameter
SS7 (Signal System No. 7) is a set of telephony protocols established in the 1970s and later standardized in the 1980s. SS7 is responsible for establishing and terminating communications primarily to 2G and 3G networks, but is still responsible for bridging communications to modern 4G and 5G networks. SS7 was developed to use “out-of-band” signalling, patching the vulnerabilities of “in-band” signalling that transmitted control signals and voice communication over the same audio frequencies. The fundamental flaw of SS7 is that it assumes everyone connecting to the network is a trusted telecommunications provider and does not include inherent authentication and encryption.
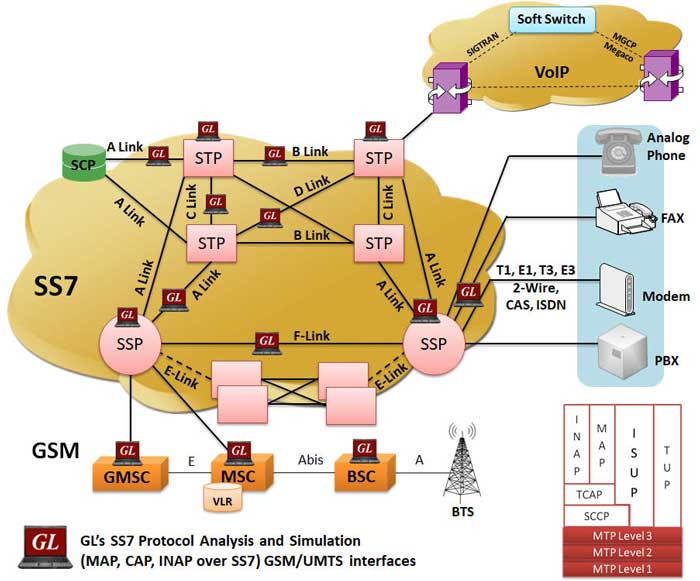
Diameter is the successor to SS7/RADIUS and acts as a AAA protocol that manages your identity on a cellular network. While SS7 orchestrated communications on 2G and 3G networks, Diameter serves as the gatekeeper for 4G and 5G LTE networks that are IP based. While Diameter supports TLS and IPsec, encryption is optional and each node needs to decrypt message data in order to read routing headers. In addition, your carrier will trust any message coming from a roaming interconnect that can be spoofed by a threat actor.
These vulnerabilities are actively exploited by most nation states for the purpose of global espionage and the tracking of high value targets. This begs the question – why don’t we replace SS7 and Diameter with modern “trustless” protocols? For a new standard to be adopted, every telecom provider on Earth would need to agree to the new protocols, tear out their existing legacy infrastructure and upgrade simultaneously without breaking interoperability. To put it simply, this isn’t possible until old technologies are phased out and old infrastructure is replaced. SS7 and Diameter will remain in place for years to come and will keep modern telecommunications vulnerable to intercept.
The Stingray Threat
Beyond the insecure network protocols underpinning the global telecom network, there are physical vulnerabilities in how data is transmitted from devices to cell towers. The GSM standards that 2G and 3G technologies rely on are inherently flawed. While a phone is required to mathematically authenticate to the network to prove a user is a paying subscriber the network itself is not required to authenticate back to the phone. This allows a threat actor to deploy a “Stingray” or IMSI catcher that masquerades as a legitimate cell tower and advertises a strong signal to your phone. Your phone will connect to the fake base station and can’t differentiate the Stingray from a legitimate cell tower. Once connected, the Stingray can extract information like your IMSI or act as a man in the middle, intercepting traffic through to the actual network while recording or modifying data.
Case Studies: Los Zetas and Mexican Cartels
Criminal Syndicates, particularly the Mexican cartels, realized early on that vulnerabilities in public telecom infrastructure can be exploited by rivals and federal law enforcement. To counter this, they have invested significant resources into building private networks that operate outside the control of the state.
These private networks started appearing when “Los Zetas” – a cartel with leadership composed of former members of the Mexican Army’s special forces – started using technologies that were previously provided by U.S. and Israeli special forces. Their military background gave them key insights into how these technologies could be used in clandestine operations. In the mid-2000s, Los Zetas began constructing a massive concealed radio network across Mexico and bordering states. This gave the Los Zetas free communication to coordinate drug shipments and monitor the locations of law enforcement or rival cartels. The construction and maintenance of these networks requires expertise that is hard to find within the ranks of a cartel, and as a result, many IT specialists were trafficked by these cartels to work on these networks full time.
The architecture of a narco-network
As the cost of radio hardware has plummeted, the cartels have built their strategy on sophisticated, software defined cellular networks. Their systems have become so state of the art that they provide a level of operational flexibility that rivals traditional mobile networks.

These networks use Software Defined Radio that allows for the creation of GSM compatible cellular networks using computers and radio peripherals. Open source software like OpenBTS was used to orchestrate these networks. Originally made to bring affordable cell service to remote areas, it was repurposed by the cartels. Peripherals like the Ettus USRP N210, a networked SDR that allowed sophisticated encryption and high speed data transfer, offered high tech at a low cost.
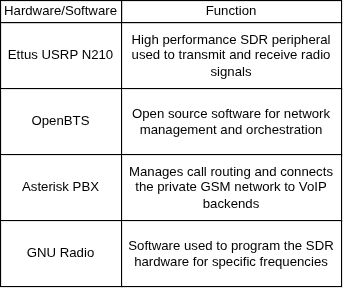
There were many environmental variables cartels had to consider; high frequencies couldn’t travel long distances and were easily blocked by terrain. Low frequencies travel much further and don’t require dense collections of cell towers. Cartels opted for lower frequencies to reduce the footprint of their infrastructure, making it harder for law enforcement to find their base stations. Sometimes parasite antennas were collocated with existing commercial towers and powered with solar panels, hiding them in plain sight.

Perhaps the most interesting method employed by cartels was how they encrypted traffic. Rather than employing standard encryption, they implemented a system of geographic and environmental authentication that is very hard to break. They used Diffie-Hellman as the key exchange algorithm, allowing two parties to establish a shared key over an insecure channel without transmitting a private key. Since Diffie-Hellman is susceptible to MITM attacks, they decided to add a system that incorporates environmental variables to randomize the generation of their keys. Keys were generated using precise GPS coordinates, exact time stamps and atmospheric conditions. The result of this key generation method was that an attacker must be physically present at the exact location, at the exact time, with knowledge of the specific environmental conditions to have any hope of intercepting the key exchange.
Low tech counterintellegence from law enforcement
Because these private networks are so robust, law enforcement agencies primarily choose to bypass intercepting communications using technology. Instead of trying to find a hole in the Cartel’s communications infrastructure, they opt for social engineering and agent infiltration. It’s true that many states have access to zero click spyware like Pegasus that can compromise an endpoint, rendering even the most secure communications protocols useless. However, these systems require exorbitant costs to purchase/maintain and require specific regulatory and geo-political green lights to be utilized effectively. As the criminal syndicates modernize and in some cases pioneer the use of communications technology, they push law enforcement to adopt risky and invasive methods that increase the cost of investigating illicit activity.

A divergence in technology
Public communications infrastructure is fundamentally vulnerable to surveillance and tracking by design and built on an obsolete model of assumed trust. It’s a system where a state or criminal actor can easily track your location or intercept your messages and phone calls. By contrast, technology developed and utilized in clandestine operations has surpassed what is publicly available. This may seem like a logical conclusion, since different applications of communications technology require varying degrees of confidentiality, but this divergence is emblematic of a larger trend. In a world where the average citizen is more vulnerable to surveillance than high level criminals, the distribution of power tilts towards those willing to adopt high tech solutions for communications and security. While publicly available services are convenient and don’t require much investment, there is another hidden cost; the ability to freely communicate without individual rights to privacy and security. This information asymmetry is not a mere technical detail. The ability to remain “private” has become the ultimate strategic advantage in an age of persistent conflict.
